Want to experience the classic Apple operating system on modern hardware? Emulating Mac OS 9 using QEMU is the way to go! This guide will guide you through the process of setting up Mac OS 9 in QEMU, from creating a virtual hard drive to installing the operating system. Let’s get started!
Prerequisites
Before you begin, make sure you have these things:
A computer that can run QEMU (macOS, Linux, or Windows).
A Mac OS 9 installation ISO (like Mac OS 9.2.2 Universal Install. Check Archive.org).
A version of QEMU with sound support (like qemu-screamer).
You should also know a bit about using the terminal.
Step 1: Install QEMU
Download and install a version of QEMU that supports PowerPC emulation. The qemu-screamer fork is recommended for better audio support.
Clone the repository:
git clone -b screamer https://github.com/mcayland/qemu qemu-screamer
cd qemu-screamer
Configure and compile:
./configure --target-list="ppc-softmmu" --audio-drv-list="coreaudio" --enable-libusb --enable-kvm --enable-hvf --enable-cocoa
make
The compiled binary will be located in qemu-screamer/ppc-softmmu/qemu-system-ppc.
Step 2: Create a Virtual Hard Drive
Use the qemu-img tool to create a virtual hard drive for Mac OS 9:
./qemu-img create -f qcow2 macos9.img 2G
Replace 2G with your desired size if needed. Mac OS 9 does not require much space, so 2 GB is generally sufficient.
Step 3: Prepare the Installation Media
Ensure you have a bootable ISO of Mac OS 9. If you do not have one, download it from resources like “Mac OS 9 Lives.” Place the ISO in an accessible directory on your system.
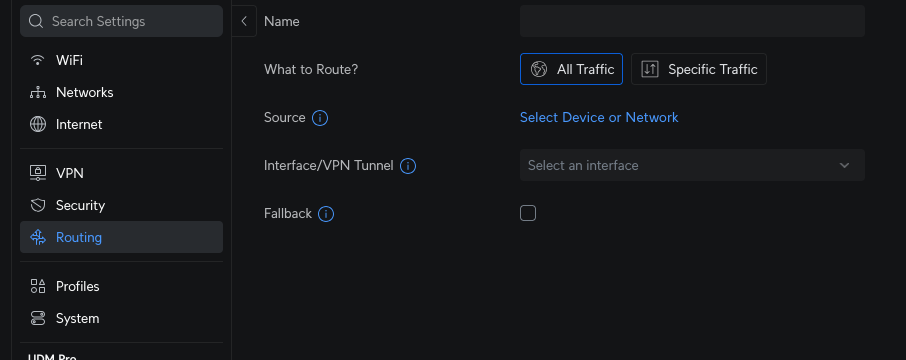
Step 4: Start QEMU and Begin Installation
Run QEMU with the following command to boot into the Mac OS 9 installer:
./qemu-system-ppc \
-L pc-bios \
-cpu g4 \
-M mac99,via=pmu \
-m 512 \
-hda macos9.img \
-cdrom "/path/to/Mac_OS_9.iso” \
-boot d \
-g 1024x768x32 \
-device usb-mouse \
-device usb-kbd
Explanation of key flags:
-cpu g4: Emulates a G4 processor.
-M mac99,via=pmu: Sets the machine type to emulate a PowerMac G4.
-m 512: Allocates 512 MB of RAM.
-hda macos9.img: Specifies the virtual hard drive.
-cdrom: Points to your Mac OS 9 installation ISO. Have a look on archive.org for the ISO.
-boot d: Boots from the CD-ROM.
Step 5: Initialize and Install Mac OS 9
Once QEMU boots, open “Drive Setup” from the Utilities folder.
Select the uninitialized disk and click “Initialize.”
Choose “Mac OS Extended” as the file system and proceed.
After initializing, return to the installer and follow on-screen instructions to install Mac OS 9 onto your virtual hard drive.
The installation process typically takes about 7–10 minutes.
Step 6: Boot into Mac OS 9
After installation is complete:
Shut down QEMU.
Modify the boot command to boot from the hard drive instead of the CD-ROM:
./qemu-system-ppc \
-L pc-bios \
-cpu g4 \
-M mac99,via=pmu \
-m 512 \
-hda macos9.img \
-boot c \
-g 1024x768x32 \
-device usb-mouse \
-device usb-kbd
Start QEMU again, and it should boot into your newly installed Mac OS 9 environment.
Optional: Enable Audio Support
If using qemu-screamer, audio can be enabled by ensuring CoreAudio is configured during compilation (–audio-drv-list=”coreaudio”). This setup allows sound output within Mac OS 9.
Tips and Troubleshooting
Backup Your Disk Image: After installation, back up your virtual hard drive (macos9.img) to avoid reinstalling if issues arise.
Adjust RAM: While Mac OS 9 can run on as little as 40 MB of RAM, allocating at least 512 MB ensures smoother performance.
Networking: Add networking support with flags like -netdev user,id=mynet and -device sungem,netdev=mynet.
By following these steps, you’ll have a fully functional emulation of Mac OS 9 running on QEMU! Enjoy exploring this nostalgic operating system.